Writeup: CSAW Quals 2019 - Beleaf
Information
- category : reverse
- points : 50
Description
tree sounds are best listened to by https://binary.ninja/demo or ghidra
Files : beleaf
Writeup
We don’t want to listen to the description because we can use the powerful cutter with the new plugin r2ghidra-dec.
After analyzing the binary with cutter and renaming some variables the main looks like this:
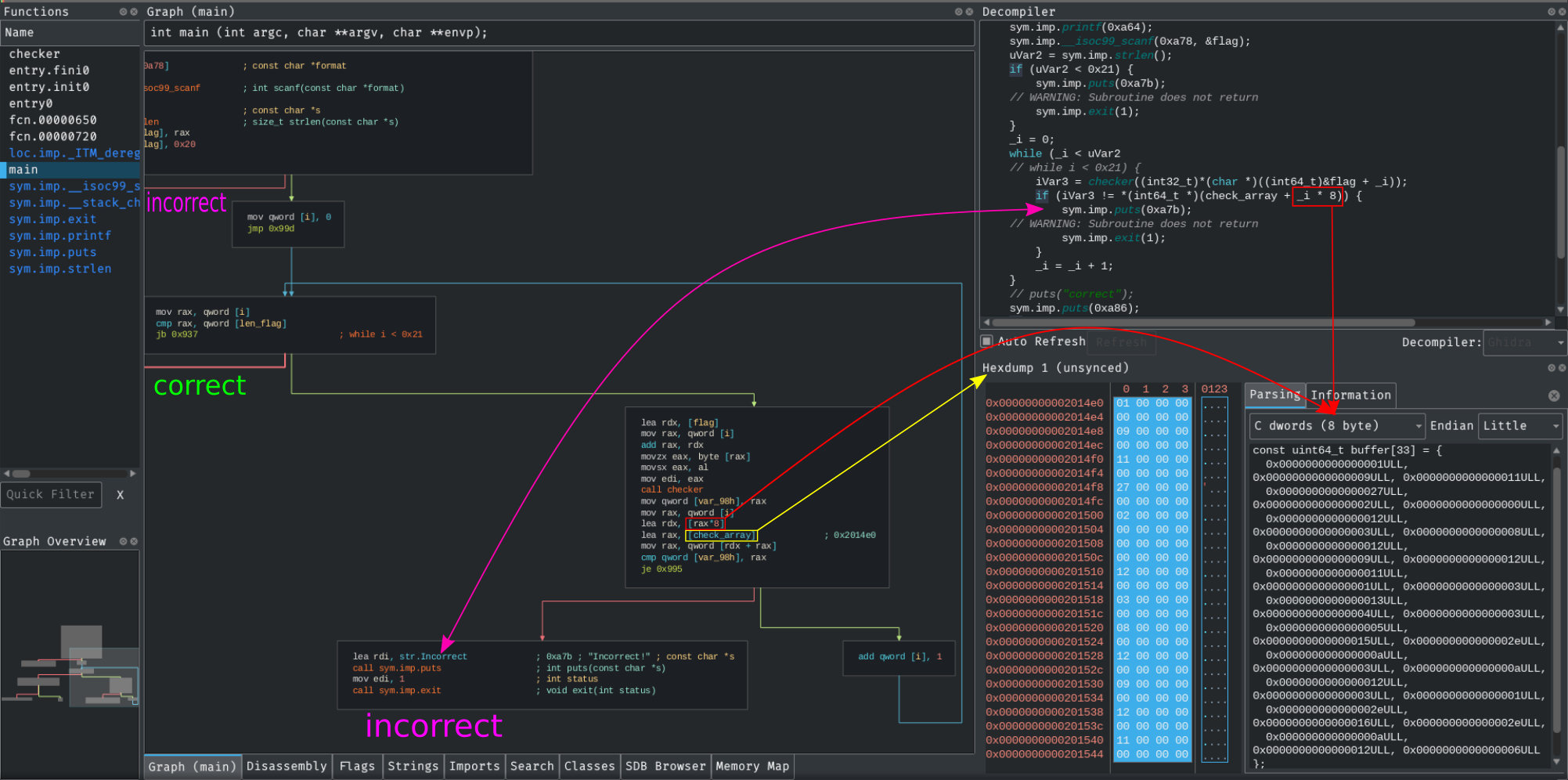
Our scope is to create an input (flag) which prints "correct". As we can see the first condition to bypass is the flag’s length that must be 0x21 = 33 or the program will execute puts(0xa7b) = "incorrect".
After the first condition we have a while that continues until i < 33.
However there’s an if statement where the program check that checker(flag[i]) == check_array[i], if this condition doesn’t hold than the program prints "incorrect" and exits.
In this case check_array is an array of long int as described in the screen (i * 8), so I opened up a new hexdump view in the address of check_array and I parsed the 33 long int into an array.
We can copy the array in a python script that later we’re gonna use and with nvim remove the lasts characters ULL –> :s/ULL//g.
Now we need to investigate what the checker function does.
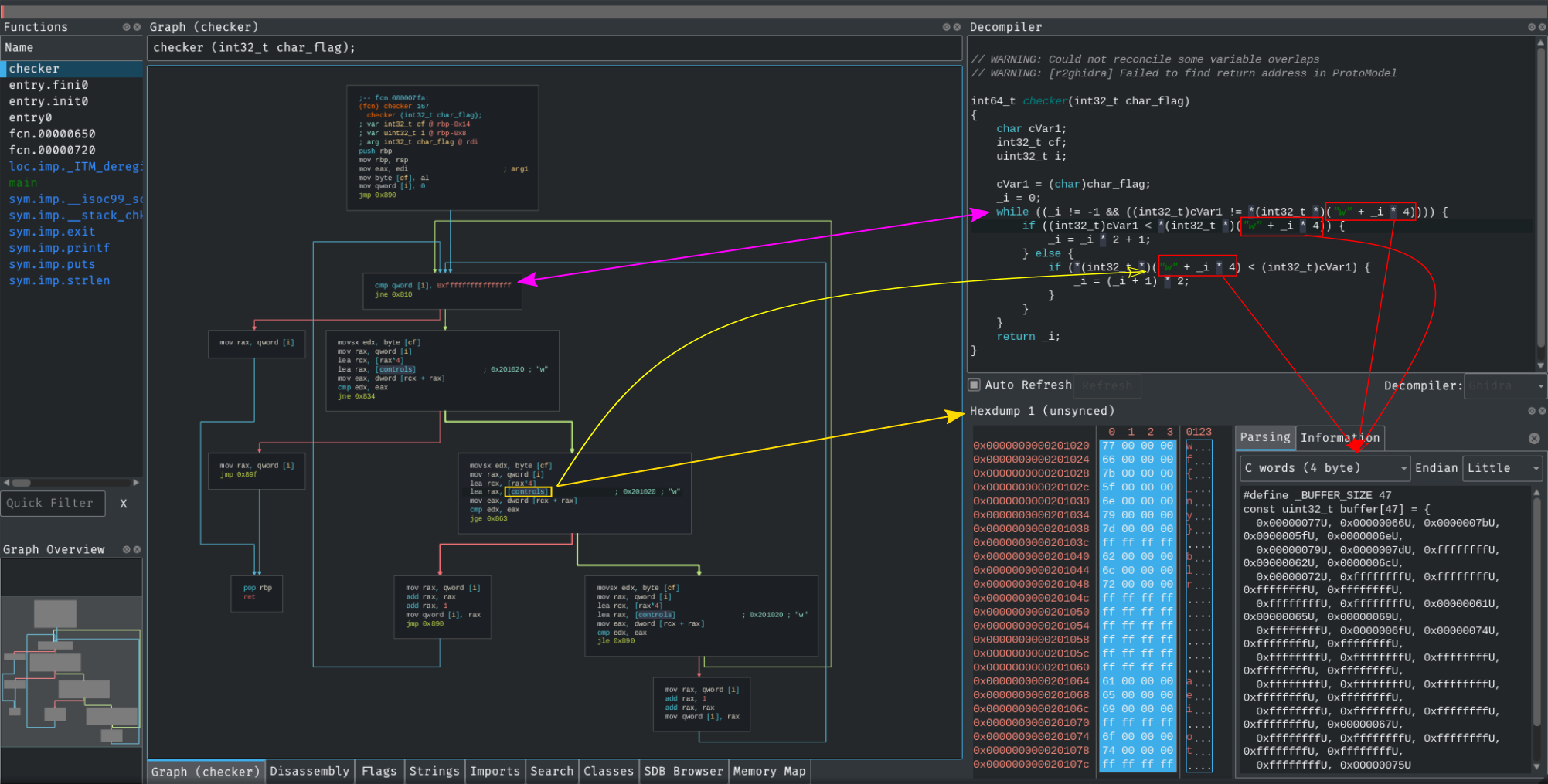
The ghidra’s decompiler in cutter parse the controls array in graph view as "w" (I will open an issue on that).
Now we can rewrite the function in pseudocode :
1 | i = 0; |
Ok so basically to stop this while iteration and return i, the characters of the flag must be the one in controls.
We can’t stop the while with the condition i != 1 because in the check_array there’s no such value as 0xffffffffffffffff.
So I parsed (again) controls to be an array of int (4 byte) using the hexdump and I copied the values in the python script.
Now we can bruteforce every character of the flag one-by-one using the following exploit.
Exploit
1 | import sys |
Flag
flag{we_beleaf_in_your_re_future}